5 Prevarications About Internet Security You’re Still Attuned to
If you’ve thought you have some peace and quiet after installing your latest top-notch and premium antivirus or cybersecurity software or passed your cybersecurity 101 course, then you should think twice, as your worries are far from being done and dusted. There are lots of assumptions and myths about internet security so often that you do not only get confused but also swim in a false sense of security, which may let you high and dry. In this article, we discuss five of them.
Recap:
Prevarication #1 There is nothing valuable on my computer
Prevarication #2 I’ve got an antivirus solution and it’s enough
Prevarication #3 If the padlock icon is present while I am surfing, then I’m safe
Prevarication #4 Only shady websites are dangerous
Prevarication #5 My device can only get compromised if I download or click on a file
Prevarication # 1: There is nothing valuable on my computer

At some point in your life, you’ve thought or think—well, nobody can go through my financial or personal data, you know, because none exists on the computer I have home—Alright. Let’s get this off the table. Unless you are still living in ‘The Flintstones’ era, high are the chances you probably send emails from it or might have applied for a job, uploaded your CV, made a purchase, or accessed your social media profile from there, which is more than enough for hackers to steal your identity and launch any type of online attacks against you.
Talk it over with yourself for a minute. Your work and life timeline are out there on the internet. And with machine learning and artificial intelligence, it is possible to get your data from a simple picture of yours. Now we’re talking, you do have something valuable on your computer and it’s worthwhile to secure.
Prevarication # 2: I’ve got an antivirus solution and it’s enough

No doubts about that, antiviruses are good to have. But again, that’s the world wide web and new viruses surface in different shapes and forms, and hackers always do their homework to find loopholes in what protects you.
Moreover, antivirus solutions only block viruses from infecting your system while you’re browsing, which is awesome, but it’s not hacking-bullet proof. Get a multi-level or multi-layer solution that possesses swarm intelligence to understand that a malicious attack is being orchestrated towards you.
Prevarication # 3: If the lock icon is Illuminated, I’m good to go!
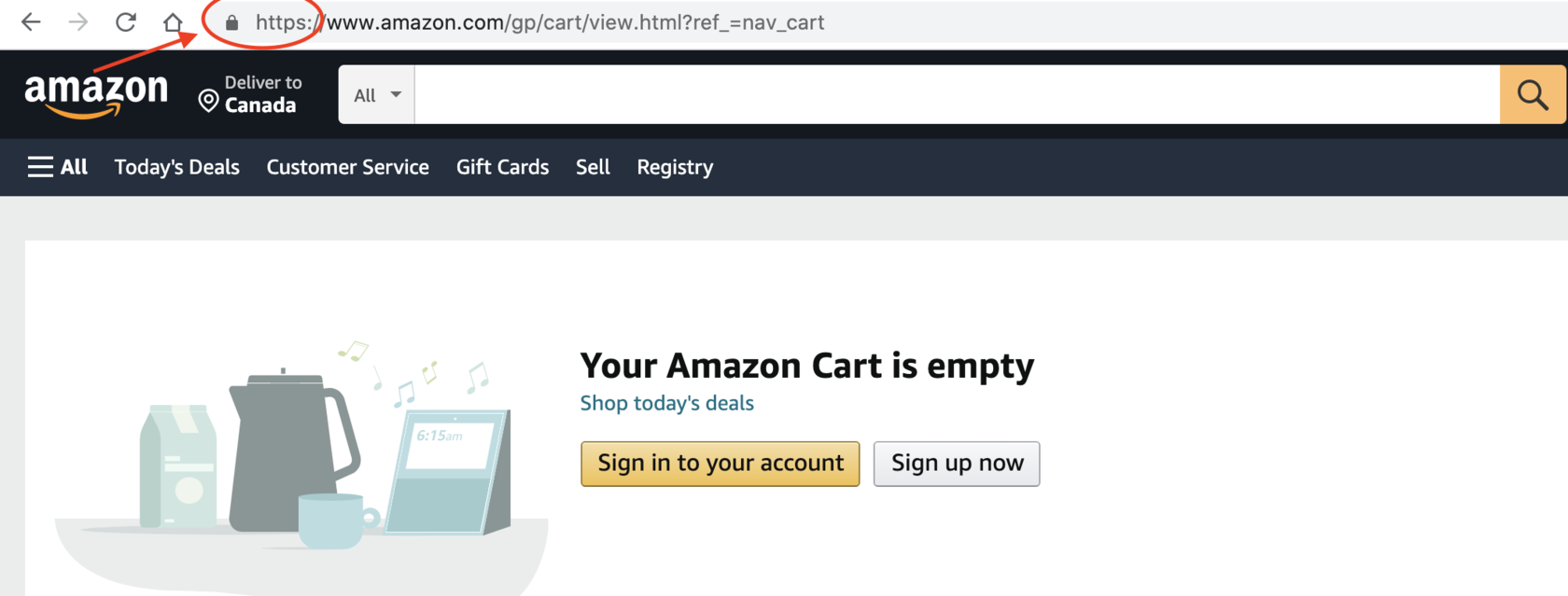
Ahem! This one might stun you, but that little padlock in the browser navbar usually followed by https—meaning there is a secure connection between the web server and your device—is not always a thing you can rely on 100% for all websites. You are less likely to encounter such an issue with sites like Amazon spending millions on cybersecurity, but you never know.
That is because you’re still not protected from malware. Also, some hackers are quite good at replicating an SSL certificate-d padlock. People fall for it thinking the page they are browsing is safe when in reality it’s not.
Prevarication # 4: Only shady websites are dangerous, wrong!

“Congratulations your number has been selected for the show! Get your 250 million dollars cash now!” If you haven’t been to gambling or weird listings websites, then lucky you! These are usually the types of messages from such sites that might pop up via a window requiring some action from you, and usually with a scammer or hacker behind all the flickering ads ready to compromise your data and computer.
However, you would be flabbergasted to know that malware attacks actually take place on legit websites, deception requires craftiness, and mostly when your guard is down, malicious attacks hit you. Always pay attention to repetitive capitalized words, the navbar, the design, and other things that might raise the red flag.
Prevarication #5: My device can only get compromised if I download or click on a file
Do you remember those days the internet was just a bric-a-brac serving email purposes, and when files with .exe were all you needed to worry about? Nowadays, everything is Cheshire-cat-like; malicious attacks might occur with the most inoffensive routine, e.g. typing your password to log in to your computer or just reading the news on the New York Times online.
You think you’re safe because nothing is transpiring when in reality you’ve already been hacked. Sometimes you notice nothing because your computer just serves as a proxy or platform to launch another malicious attack. For instance, keyloggers can go unnoticed to serve such a proxy or hacking purpose, and occasionally, may require the reformatting of your entire computer to get rid of it.
Take-away for online shoppers:
When you click on the button ‘buy’, ‘order’, or ‘purchase’ for the items you added to your cart, and the page instead of showing a message indicating a successful purchase shows an error message or takes time to load, that might be a sign that the website you are on has been infected by a Distributed Denial of Service Attack (DDoS) or other malware.
Hopefully, it is just an internet connection issue. However, if all technical things are considered, then you should worry and double-check with your credit/debit card issuer that no suspicious activities have taken place on your side, of course after unlinking your card from that online shop payment methods.
You can get a free online protection with SafeDNS for 15 days. This will ensure that you stay safe while browsing the internet.
Take advantage of the SafeDNS trial period and try all the best features

