
Why NGFWs Can’t Detect Stealth DNS Attacks (and How to Close the Gap)
Next-Generation Firewalls (NGFWs) are a cornerstone of enterprise network security, offering advanced features like deep packet inspection, intrusion prevention, and application-layer filtering. However, when it comes to detecting stealth DNS attacks, such as covert data exfiltration, domain generation algorithm (DGA)-based attacks, and command-and-control (C2) communication hidden in DNS traffic, NGFWs often fall short. This article explores the technical limitations of NGFWs in addressing these threats, provides detailed examples of stealth DNS attack techniques, and explains how SafeDNS’s DNS resolution-based security solutions close these critical gaps.
The Growing Threat of Stealth DNS Attacks
DNS is the backbone of internet communication, translating human-readable domain names into IP addresses. Its ubiquitous nature makes it an attractive vector for attackers. Stealth DNS attacks exploit this protocol to bypass traditional security measures, including NGFWs, by hiding malicious activities within seemingly legitimate DNS traffic. These attacks are particularly dangerous because they can facilitate data exfiltration, malware propagation, and persistent C2 communication without triggering alerts.
NGFWs, despite their sophistication, struggle to detect these attacks due to limitations in their architecture and focus. So let us break down why NGFWs are ill-equipped to handle stealth DNS threats and provide examples of common attack techniques.
Why NGFWs Struggle with Stealth DNS Attacks
1. Encrypted DNS Traffic
With the rise of DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT), DNS queries are increasingly being sent in encrypted form. That’s great for user privacy, but not so great for visibility. To an NGFW, encrypted DNS traffic looks like regular HTTPS. Unless you’ve deployed SSL inspection (which many organizations avoid due to complexity or privacy concerns), the firewall simply can’t see what’s inside those packets.
2. DNS Tunneling and Obfuscation
DNS tunneling allows attackers to slip data through a channel that’s rarely scrutinized. Firewalls typically allow DNS traffic by default, and most don’t deeply inspect the protocol. That means encoded payloads, whether for exfiltration or C2 communication, often go unnoticed. Unless an NGFW is doing full DNS protocol parsing and behavioral analysis (which most aren’t), it will likely miss this entirely.
3. Limited DNS-Specific Analysis
NGFWs are designed for broad-spectrum threat detection, such as identifying malware signatures or blocking unauthorized applications. However, they often lack specialized DNS analysis capabilities. Stealth DNS attacks exploit subtle patterns, such as unusual query frequencies or domain name structures, which require dedicated DNS monitoring tools to detect effectively.
4. Overwhelming DNS Traffic Volume
DNS traffic is high-volume and constant in enterprise networks, making it challenging for NGFWs to analyze every query without impacting performance. Attackers exploit this by blending malicious DNS activity into the noise of legitimate traffic, using low-and-slow techniques to avoid detection.
5. Evolving Attack Techniques
Many NGFWs rely on rule sets, threat signatures, or blocklists that must be updated regularly. But stealthy DNS-based threats don’t always show up in those feeds, especially if they’re using DGAs or fast-flux infrastructure. Attackers can pivot and adapt much faster than static defenses can keep up.
6. Lack of Contextual and Behavioral Analysis
Stealth DNS attacks often involve distributed, low-frequency patterns that are difficult to detect without long-term behavioral analysis. NGFWs may not have the machine learning or correlation capabilities needed to identify these subtle anomalies over time.
Examples of Stealth DNS Attack Techniques
To understand the challenges NGFWs face, let’s examine three common stealth DNS attack techniques, their mechanics, and why they evade traditional firewall defenses.
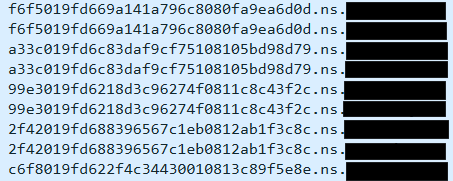
1. DNS Tunneling
DNS tunneling encodes sensitive data (e.g., stolen credentials or intellectual property) into DNS queries or responses. For example, an attacker might encode data in the subdomain of a DNS query, such as ZW5jcnlwdGVkLWRhdGE.tunnel.attacker-domain.com. The DNS resolver, controlled by the attacker, responds with encoded instructions or acknowledgments. Since DNS queries are typically allowed through firewalls, this traffic often goes unnoticed. The same method can be used for data infiltration as well, for example requesting it via the Cname or TXT, MX fields allowing to cut to batches send and assemble tools that will be used for attacks internally.
For example the DNScat2 framework uses DNS tunneling to exfiltrate data. It breaks down stolen data into small chunks, encodes them as subdomains, and sends them as DNS queries.
And since NGFWs don’t deeply inspect DNS payloads (especially if encrypted), they often miss this entirely.
The lack of deep DNS protocol inspection needed to decode and analyze subdomain payloads is one of the reasons that NGFWs fail to stop such attacks? While even if they detect unusual query patterns, the encrypted nature of such traffic obscures the malicious content. The widely known from the “SolarWinds” case, “SUNBURST” malware used DNS tunneling to exfiltrate data to the C2. While APT 34 also known as “OilRig” are known for their tendency to use the DNS tunneling for network mapping and recon.
2. Domain Generation Algorithms (DGAs)
DGAs are used by malware to generate thousands of pseudo-random domain names, only a subset of which are registered by the attacker for C2 communication. This makes it difficult for security tools to block malicious domains, as the malware dynamically switches between domains. For example, a DGA might generate domains like x7b9p2q.attacker.com or k3m8v9r.attacker.com based on a seed value, such as the current date or other less predictable values such as a currency exchange course or a word from a top comment on a social network.
The infamous “Conficker” worm, a well-known malware, used a DGA to generate up to 50,000 domains daily, only a few of which were used for C2. This overwhelmed traditional blocklists, which made blocking domains based on IOC feeds impossible and led to a large joined campaign of some of the largest industry companies to stop the worm from spreading. And yet even today (almost 20 years after) estimates of 300-500k hosts in the world are still infected.
To effectively counter DGAs today, it is recommended to employ DNS traffic analysis in combination with AI-driven techniques, such as N-Gram analysis or WordGraph-based models, which can identify and block algorithmically generated domains in real time.
3. Fast-Flux DNS for C2 Communication
Fast-flux DNS rapidly changes the IP addresses associated with a domain name, often using a network of compromised hosts. This technique hides the true location of C2 servers, making it difficult to block or trace the attacker’s infrastructure. DNS responses return different IPs for the same domain in rapid succession, often within minutes.
A well-known example is the Storm botnet, which used fast-flux DNS to maintain a highly resilient and decentralized C2 network. By the time defenders identified and blocked one IP, the domain had already rotated to another, keeping the malware one step ahead of traditional defenses.
Closing the Gap
This is where DNS-layer security platforms like SafeDNS really shine. Instead of trying to filter DNS traffic at the perimeter or after the fact, they intercept queries right at the resolution stage, before any connection to a domain is ever made.
A dedicated DNS-layer security solution offers several advantages when it comes to addressing stealth DNS threats that typically bypass NGFWs. By analyzing DNS queries in real time, such solutions can detect anomalies like unusual query patterns, high-frequency lookups, or suspicious domain structures that may indicate tunneling or algorithmically generated domains. Instead of relying on post-resolution detection, DNS-layer protection works at the resolution stage - preventing connections to malicious domains before they’re established. This early intervention is especially useful against malware that frequently changes command-and-control infrastructure. DNS-layer tools also provide much-needed visibility into network activity from unmanaged or IoT devices, which often operate with limited oversight and can become entry points for covert communication or data exfiltration. Leveraging machine learning, these solutions can spot subtle behaviors such as low-and-slow tunneling or fast-flux techniques, adapting to evolving threats with the help of real-time threat intelligence. Because they focus exclusively on DNS traffic, these tools are typically designed to scale efficiently, allowing for deep inspection of high query volumes without degrading network performance, making them particularly well-suited for modern enterprise environments.
Practical Steps for Enterprises
Modern cyber threats increasingly rely on stealth, persistence, and multi-stage tactics that can bypass single-point defenses. To counter this, enterprises should adopt a defense-in-depth approach – layering multiple, complementary security controls across the infrastructure to detect, prevent, and respond to threats at every stage.
Key practices include:
- Implement Layered Network Security: Combine perimeter defenses like next-generation firewalls (NGFWs) with internal segmentation, intrusion detection systems (IDS/IPS), and endpoint protection to limit the impact of breaches and lateral movement.
- Deploy DNS-layer Protection: Implement DNS security solutions that monitor, filter, and block malicious domain requests at the resolution stage, reducing the risk of phishing, malware callbacks, and command-and-control (C2) communications.
- Inspect Encrypted Traffic: With the rise of encrypted protocols (e.g., TLS, DoH, DoT), organizations must maintain visibility through SSL inspection, endpoint telemetry, or traffic analysis tools that preserve privacy while identifying threats.
- Integrate Threat Intelligence: Use up-to-date threat intelligence from diverse sources to enrich detection and automate blocking of known malicious indicators across email, web, DNS, and endpoints.
- Centralize Logging and Monitoring: Aggregate security telemetry from across the environment (network, DNS, endpoints, cloud) into a centralized SIEM or XDR platform for correlation, detection of anomalies, and incident response.
- Continuously Educate and Train Staff: Keep security teams informed about evolving attack techniques and empower employees with security awareness training to reduce human error and social engineering risk.
- Conduct Regular Security Audits: Validate the effectiveness of controls through continuous monitoring, red teaming, and periodic risk assessments to identify gaps and prioritize remediation.
Conclusion
At SafeDNS, we adhere to the concept of defense in depth. And while NGFWs (Next-Generation Firewalls) are powerful tools for network security, both research and practical experience show that DNS plays a critical role in today’s cyber threat landscape. That’s why, within a multi-layered security architecture, it is essential to give special attention to dedicated DNS security solutions.
Take advantage of the SafeDNS trial period and try all the best features

